My New Business Venture: BlueSteel Cybersecurity Launches Advanced Cybersecurity & CMMC Services

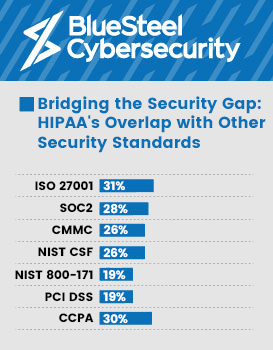
Bridging the Security Gap: HIPAA’s Overlap with Other Security Standards
No matter what industry you are in, cybersecurity has a cost, and it occasionally has an unforeseen cost. These days, it seems like a new cybersecurity compliance is released every week, and in order to keep doing business with your clientele, you must be fully compliant. The underlying question is: What is the best time and money-efficient method of managing security programs? For the majority of firms, this may be daunting and expensive in terms of both time and money.
We must first understand what is necessary to create an effective security compliance program. The development of an efficient cybersecurity program for your business necessitates the coordination of human, technological, and intellectual resources. The main categories of resources you would want are listed below:

Personnel:
- Cybersecurity Analysts: Skilled professionals responsible for monitoring and analyzing security systems, identifying vulnerabilities, and responding to security incidents.
- Security Engineers: Experts who design and implement security solutions, such as firewalls, intrusion detection systems, and encryption protocols.
- Incident Responders: Specialists who handle and mitigate security incidents promptly, minimizing potential damage and facilitating recovery.
- Security Operations Center (SOC) Manager: Oversees the team, manages resources, and ensures effective coordination of security operations.
- Chief Information Security Officer (CISO): Provides strategic guidance, develops security policies, and ensures compliance with industry regulations.
- Security Awareness Trainers: Educate employees about cybersecurity best practices and help foster a security-conscious culture within the organization.
- Legal and Compliance Experts: Ensure the company adheres to relevant laws, regulations, and data protection requirements.

Technology Resources:
- Security Information and Event Management (SIEM) System: Collects and analyzes security event data from various sources, enabling proactive threat detection and response.
- Intrusion Detection/Prevention Systems (IDS/IPS): Monitor network traffic for suspicious activity and can take automated actions to block or alert on potential threats.
- Firewall and Network Security Appliances: Protect the company’s network infrastructure by filtering and controlling incoming and outgoing traffic.
- Endpoint Protection Solutions: Antivirus software, host-based firewalls, and other tools that secure individual devices (e.g., laptops, desktops, mobile devices).
- Vulnerability Assessment and Penetration Testing Tools: Identify weaknesses in systems and applications, enabling proactive remediation.
- Data Loss Prevention (DLP) Solutions: Monitor and control sensitive data to prevent its unauthorized disclosure or loss.

Knowledge Resources:
- Training and Certifications: Invest in training programs and certifications for your cybersecurity team members to enhance their skills and keep them updated on the latest threats and technologies.
- Threat Intelligence: Subscribe to threat intelligence services that provide up-to-date information on emerging threats, vulnerabilities, and attack techniques.
- Industry Standards and Best Practices: Stay informed about cybersecurity frameworks (e.g., NIST Cybersecurity Framework) and adopt best practices to ensure a robust security posture.
- Collaboration and Information Sharing: Encourage your team to participate in industry forums, conferences, and information sharing communities to learn from peers and experts.
The three (3) methods listed below can help any organization record the necessary information and associated costs:
DIY (Do It Yourself)
Although it will be the most expensive option, it provides the chance to create an internal staff dedicated to the company’s security compliance. There is an advantage to developing an internal team to keep everything in-house if your company anticipates that security will be a crucial factor in the organization’s performance and has the capacity to boost prices to accommodate the higher expenditures.
Minimum Annual Budget: $300,000/year.
Pro: Investing in internal resources for the long run.
Cons: High human and technology costs, insufficient work, and insufficient challenges to keep workers interested.
DIWY (Do It With You)
This route, which is also regarded as a hybrid approach, gives you the chance to lower internal resource costs by collaborating with a partner who can offer personnel augmentation and technology savings. Although this solution is not the least expensive, it offers the greatest balanced use of both internal and external resources.
Minimum Annual Budget: $175,000/year.
Pro: Possibility to develop long-term internal resources and receive outside assistance.
Cons: Not the most affordable choice, requires continued use of internal security resources
DIFM (Do It For Me)
A security partner will supply the necessary resources as part of a full outsourcing solution. The firm can delegate duties to experts or specialized service providers, freeing up its employees to concentrate on their core skills or enjoy their leisure time.
Minimum Annual Budget: $48,000/year.
Pro: Lower overall expenses and internal costs
Cons: Internal resource development is not ongoing.
It is clear that a DIFM (Do It For Me) or fully outsourced option is the least expensive on the basis of cost alone. That is understandable given that the majority of cybersecurity suppliers (including us) are entirely focused on creating efficient processes and procedures that can be employed with each new customer we onboard. The other aspect is that we can split the expense of our technological solutions among our clientele base, which enables us to offer high-end solutions for a much lower price.
What is the ultimate objective for your company, cost considerations aside? Is the goal to create an internal security program that will eventually add value to your product, or is it to fulfill external security criteria in order to avoid potential sales barriers?
According to our experience, developing an internal security program makes the most sense for a company that has security as a roadmap approach to give as a future service to their consumers. The best option for organizations who want to meet their security demands while keeping their attention on what they do best (and are not interested in future security offerings) is to work with a security provider who offers the following:
- Know the inner workings of your firm and its culture. By doing this, you may increase the security program’s return on investment for your organization and figure out how to design a friction-less program for your staff.
- Aims to increase productivity by utilizing cutting-edge technologies and automation where necessary.
- Committed to security compliance and has the track record of compliance success for similar organizations.
- Focused on your sector to be able to anticipate future regulatory compliance requirements.
- Possess the partnerships and skill set necessary to meet all of your security operation’s demands.
There is ultimately no easy, universal solution. Everything depends on the goals of your company and the established competitive tactics for your market. What we do know is security is becoming increasingly important and will continue to create more pressure for those who don’t have a program in place.
If you have questions or need some advice, please message me on LinkedIn.